Want the IRM weekly cybersecurity roundup sent straight to your inbox? Sign up to our newsletter.
Emergency Microsoft IE patch update released
A Microsoft IE patch update has been issued after two flaws were discovered in its software.
The first flaw is a critical Microsoft IE zero-day that cybercriminals are already exploiting. The vulnerability is a memory-corruption issue. This means a remote attacker could hijack a Windows PC by convincing the user to view a bugged web-page.

This vulnerability affects Microsoft IE version 9 through 11, although Microsoft has not released details of the exploitation. It is recommended that those using IE 9-11 should use alternatives such as Google Chrome or Mozilla Firefox.
Another security patch is for a DoS (Denial of Service) vulnerability in Microsoft Defender, the anti-malware engine on versions 8+ of Microsoft.
According to advice published by Microsoft, an attacker could exploit this vulnerability “to prevent legitimate accounts from executing legitimate system binaries”. But in order to exploit this flaw, the attacker would “first require execution on the victim system.” You can read more here.
High-profile YouTube channels hit by cybercriminals
High-profile YouTube accounts have recently been hijacked by what seems to be a coordinated cybercriminal campaign using phishing sites.
YouTube has been inundated with complaints on their support page regarding hacked YouTube user channels and inability to access accounts.
The high-profile accounts seem to mostly come from the automotive and car-reviewing community.
The phishing attacks were used to steal the credentials of the YouTube channel owners. They revealed the hackers sent emails to lure them to phishing sites which looked like Google login pages.
The attackers used these details to log into users Google accounts and re-assign the channels to new owners. They also changing the “Vanity URL” which makes it look like the channel and account had been deleted. These have since been found available for sale on Dark Net forums. You can read more here.
Hacker group ‘GandCrab’ has resurfaced
The notorious hacker group “GandCrab” has resurfaced after a new series of attacks across the world.
GandCrab are known for selling customised ransomware to other criminals. It is estimated that their coding has affected over 1.5 million machines, including in hospitals.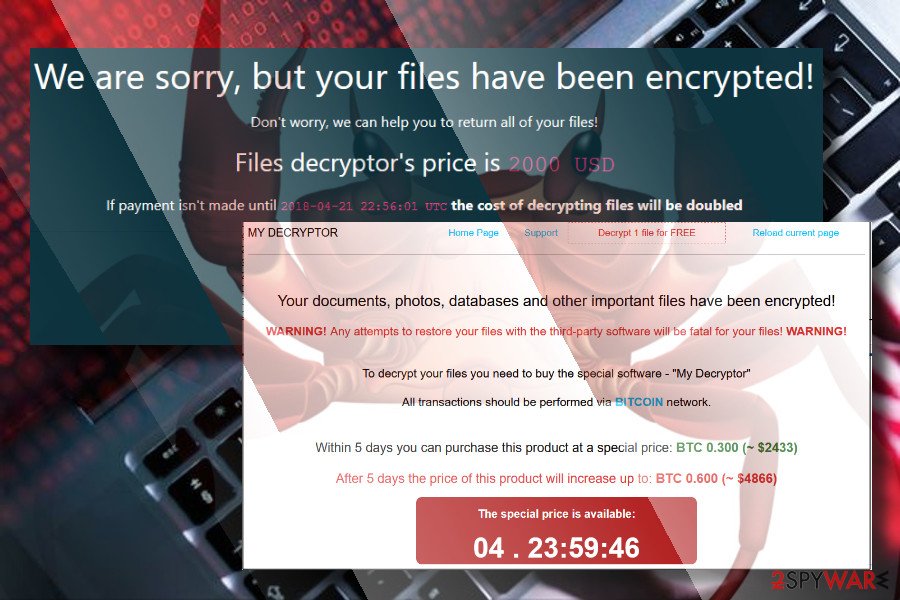
The group had “retired” after earning more than £1.6bn from the trade. Until recently, when a cybersecurity company found a new strain of computer viruses and connection mistakes similar to GangCrabs’ style.
The new strain of Ransomware, called “Revil or Sondinobiki” has caused major disruption to hundreds of dental practices in the US along with 22 Texas municipalities. You can read more here.
Quick-fire Updates:
Home security gadgets are vulnerable to hackers: A family allowed a group of hacking experts to infiltrate their gadgets for research into vulnerabilities. They were able to listen to private conversations through a tracker for older people and spy on the family through the “pet cam”. You can read more here.
Scammers targeting vulnerable Thomas Cook holidaymakers: Scammers are targeting those who have lost money from the cancellation of Thomas Cook flights and packages. They are asking for bank details to “refund” customers. You can read more here.
US entities are being targeted by state-backed attackers: Roughly 17 US utility providers have been targeted by a spear-phishing campaign in the last five months. The phishing messages attempted to infect targets with remote access Trojan called LookBack. You can read more here.
